Get instant access to experienced compliance experts, supported by a platform that automates risk assessments, evidence collection, and security awareness training. The CISO-built platform for risk management.
4.9
rating on

Top-rated on G2 — thanks to our customers.







80%
CyberUpgrade automates up to 80% of compliance tasks to reduce team workload.
60,000€
CyberUpgrade cuts compliance costs by over €60,000 each year.
24/7
CyberUpgrade keeps you audit-ready 24/7—no last-minute stress.
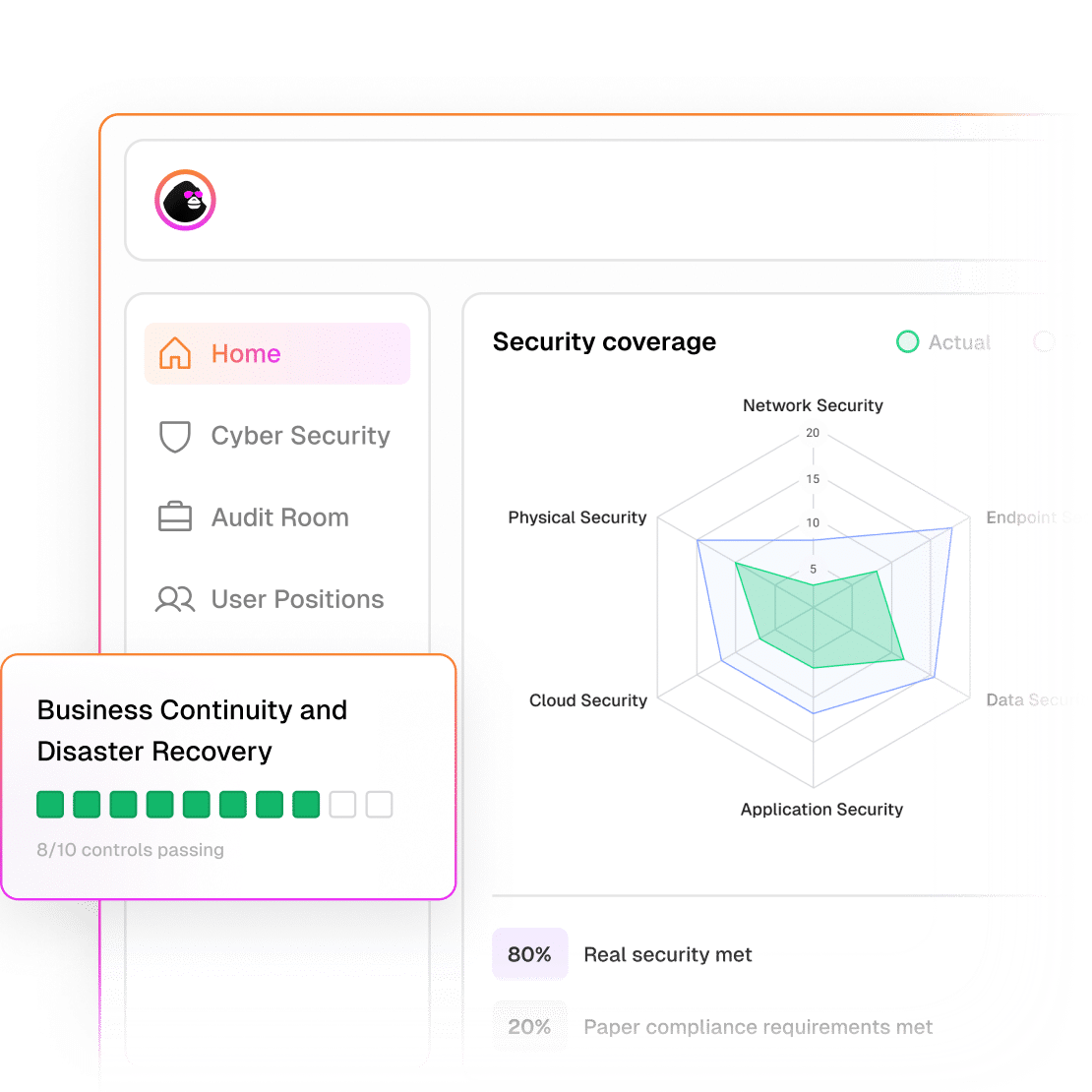
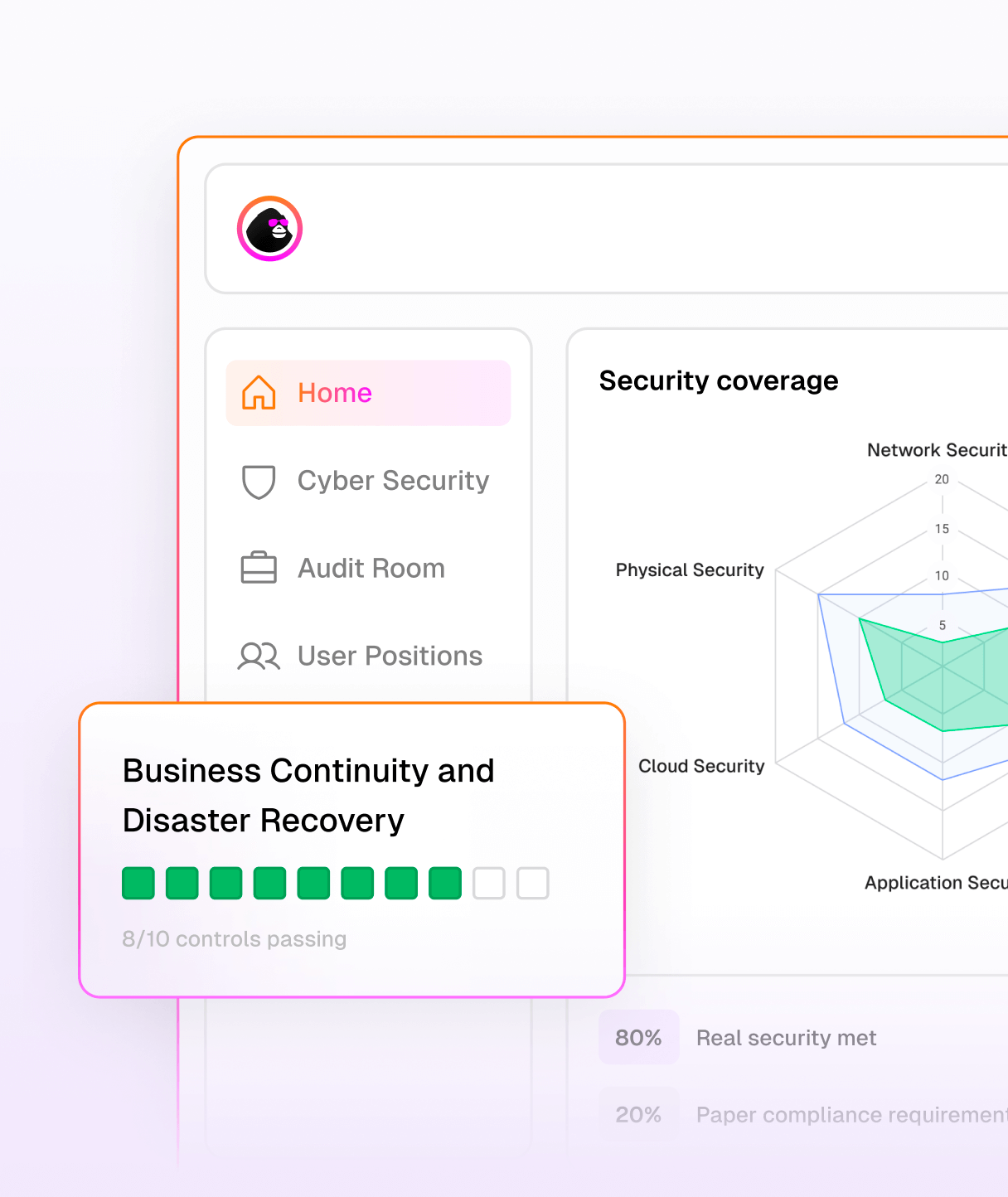
Automate evidence collection for compliance frameworks like NIS2, DORA, SOC 2, ISO 27001, GDPR, and more — complete with built-in vulnerability scanning and pentest management.
Move beyond point-in-time assessments with continuous controls monitoring, risk management, and built-in security awareness training to keep your team audit-ready.
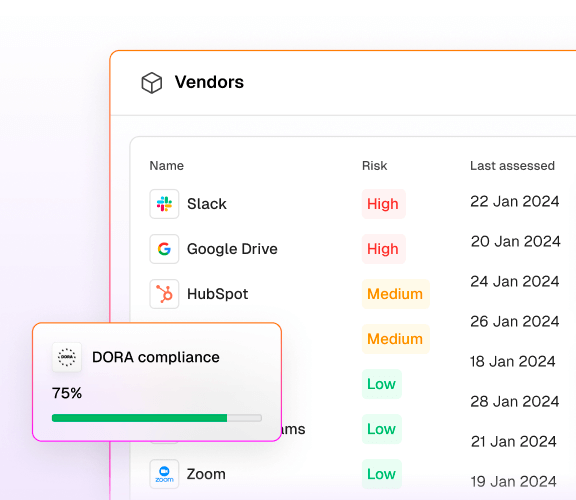
Safely introduce cutting-edge software to your business by identifying and monitoring vendor risk and protecting customer data.
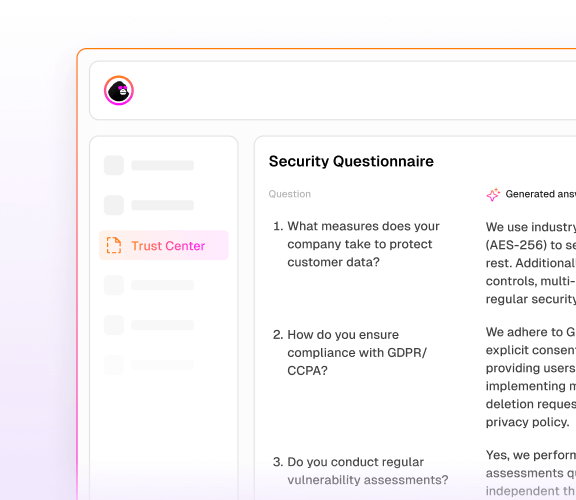
Complete security reviews up to five times faster with AI-powered security questionnaires and trust centers.
Every compliance framework comes with requirements, detailed controls, and often hundreds of tasks needed to demonstrate compliance. Our platform and experts simplify this process — helping you complete the necessary steps and achieve full compliance faster.

Not everything can (or should) be automated. That’s why we pair each customer with a fractional CISO who tailors the approach to your business reality. Kickstart the process with either our risk assessment chatbot or a personalized expert review—both paths deliver clear, practical guidance toward ICT compliance.

aiCTO at Whatagraph
We couldn't have done this without our guides throughout this process CyberUpgrade and their amazing team.
Data security has always been a top priority for us. That’s why we partnered with CyberUpgrade, whose expertise helped ensure we met every requirement. This certification proves our commitment to securing data and building trust with our clients and partners.
A big thank you to CyberUpgrade, Aurimas Bakas, and Zbignev Zalevskij for their invaluable support throughout this process!

aiCTO at Whatagraph
We couldn't have done this without our guides throughout this process CyberUpgrade and their amazing team.
Data security has always been a top priority for us. That’s why we partnered with CyberUpgrade, whose expertise helped ensure we met every requirement. This certification proves our commitment to securing data and building trust with our clients and partners.
A big thank you to CyberUpgrade, Aurimas Bakas, and Zbignev Zalevskij for their invaluable support throughout this process!
Automatically collects and stores all compliance evidence in one place for auditors.
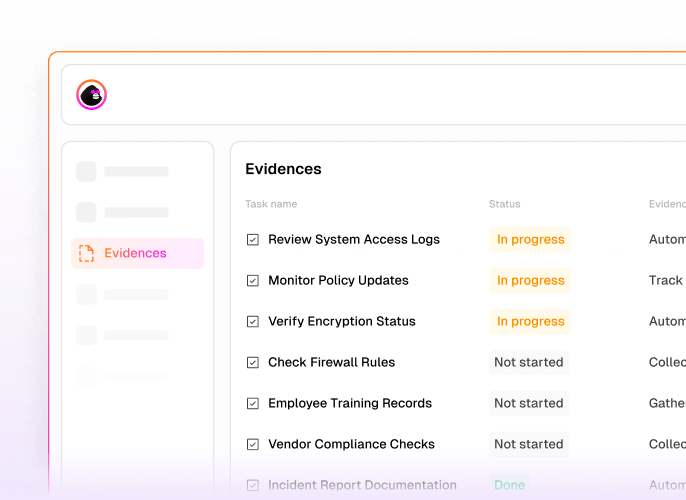
Guides you through compliance tasks using workflows and collects evidence for each task.

Automate compliance with predefined or customizable workflows, eliminating manual checking of compliance requirements.
For companies, CyberUpgrade is like a full in-house cybersec & compliance team for a fraction of the cost.
You shouldn’t have to become a compliance expert to grow your business. We handle the complexity of frameworks like DORA, ISO 27001, and NIS2—so your team can stay focused on building, scaling, and serving your customers.
Get certified faster with automation-driven workflows and expert support that eliminate bottlenecks and delays.
Work alongside seasoned CISOs who tailor your compliance strategy and support you every step of the way.
Offload up to 80% of manual tasks with streamlined evidence collection, task assignment, and policy management.
Avoid the overhead of hiring dedicated security staff while still meeting the highest regulatory standards.
Let your team focus on what they do best—while we manage the controls, documentation, and audit readiness.
We represent your company in auditor interactions and help you navigate the process smoothly—minimizing delays, confusion, and overhead.

Compliance analysis
Automated evidence collection
Data extraction & Risk assessment
Policy & Documentation setup
Risk management & Security workflows
Continuous monitoring & Reporting
We comprehensively review your processes, controls, and documentation for full compliance alignment. Our platform identifies and prioritizes gaps by risk, provides targeted recommendations, and customizes controls to your operations, establishing clear compliance goals.

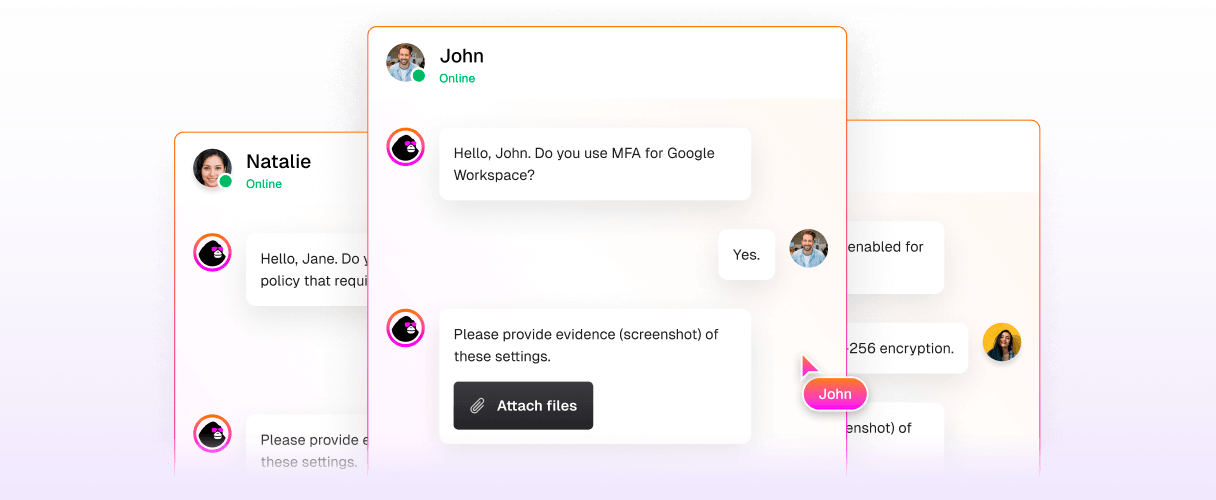
Our proactive security platform automatically gathers compliance evidence directly through Slack and Teams, continuously assessing your readiness against critical regulations in real-time—so you can maintain compliance effortlessly.

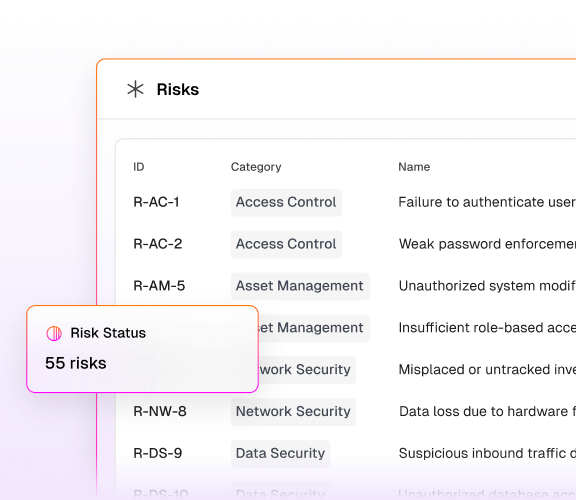
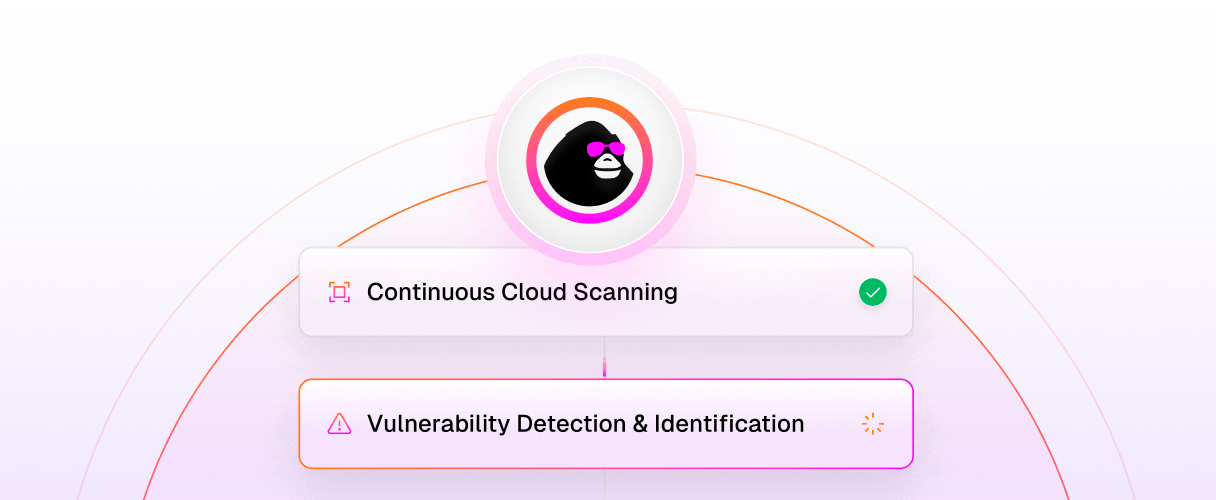
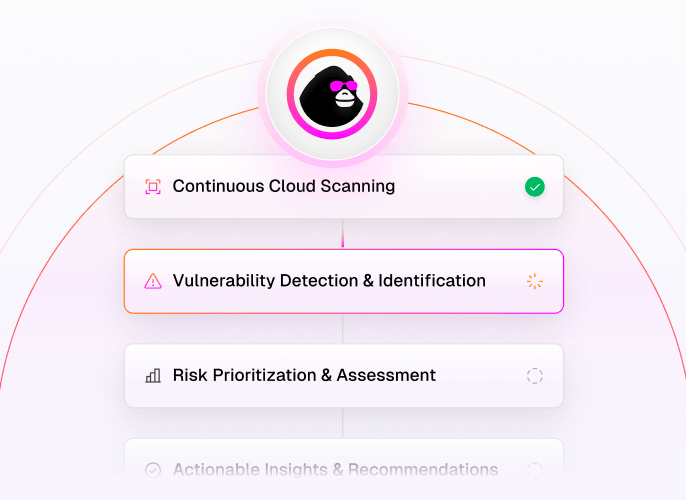
Our cybersecurity evidence engine automatically extracts relevant data—from logs and user inputs to critical documentation—and benchmarks it against compliance requirements. It flags and categorizes vulnerabilities by severity, delivering concise reports to efficiently address compliance gaps.

CyberUpgrade simplifies policy creation with ready-to-use templates specifically designed for your compliance needs. Documentation is automatically captured, eliminating the tedious process of manual collection and storage.

We’ve built hundreds of automated security and compliance workflows safeguarding your operations daily. These handle resource-intensive tasks like team training by proactively engaging every employee, ensuring robust compliance without extra workload.

Our platform continuously monitors data from all your systems, delivering a real-time view of your security posture. It also generates dynamic, automated reports that translate raw data into actionable insights.

Compliance analysis
We comprehensively review your processes, controls, and documentation for full compliance alignment. Our platform identifies and prioritizes gaps by risk, provides targeted recommendations, and customizes controls to your operations, establishing clear compliance goals.

Automated evidence collection
Our proactive security platform automatically gathers compliance evidence directly through Slack and Teams, continuously assessing your readiness against critical regulations in real-time—so you can maintain compliance effortlessly.

Data extraction & Risk assessment
Our cybersecurity evidence engine automatically extracts relevant data—from logs and user inputs to critical documentation—and benchmarks it against compliance requirements. It flags and categorizes vulnerabilities by severity, delivering concise reports to efficiently address compliance gaps.

Policy & Documentation setup
CyberUpgrade simplifies policy creation with ready-to-use templates specifically designed for your compliance needs. Documentation is automatically captured, eliminating the tedious process of manual collection and storage.

Risk management & Security workflows
We’ve built hundreds of automated security and compliance workflows safeguarding your operations daily. These handle resource-intensive tasks like team training by proactively engaging every employee, ensuring robust compliance without extra workload.

Continuous monitoring & Reporting
Our platform continuously monitors data from all your systems, delivering a real-time view of your security posture. It also generates dynamic, automated reports that translate raw data into actionable insights.

Discover how companies across industries automate compliance, cut costs, and stay audit-ready with CyberUpgrade.

Audrius Dumbliauskas
HeavyFinance Product Manager

Jēkabs Hincenbergs
Co-founder & CTO at Swotzy
Testimonials
Top-rated on G2 — thanks to our customers.


Audrius Dumbliauskas
HeavyFinance Product Manager

Jēkabs Hincenbergs
Co-founder & CTO at Swotzy